How to Configure Single Sign-On (SSO) with Microsoft Azure Active Directory?
We will go over how to configure SAML-based Single Sign-On (SSO) with Microsoft Azure Active Directory in this post.
If you use Okta for SSO, refer to: How to Configure Single Sign-On (SSO) with Okta.
If you use Google for SSO, refer to: How to Configure Single Sign-On (SSO) with Google.
Create an enterprise application in Azure Active Directory
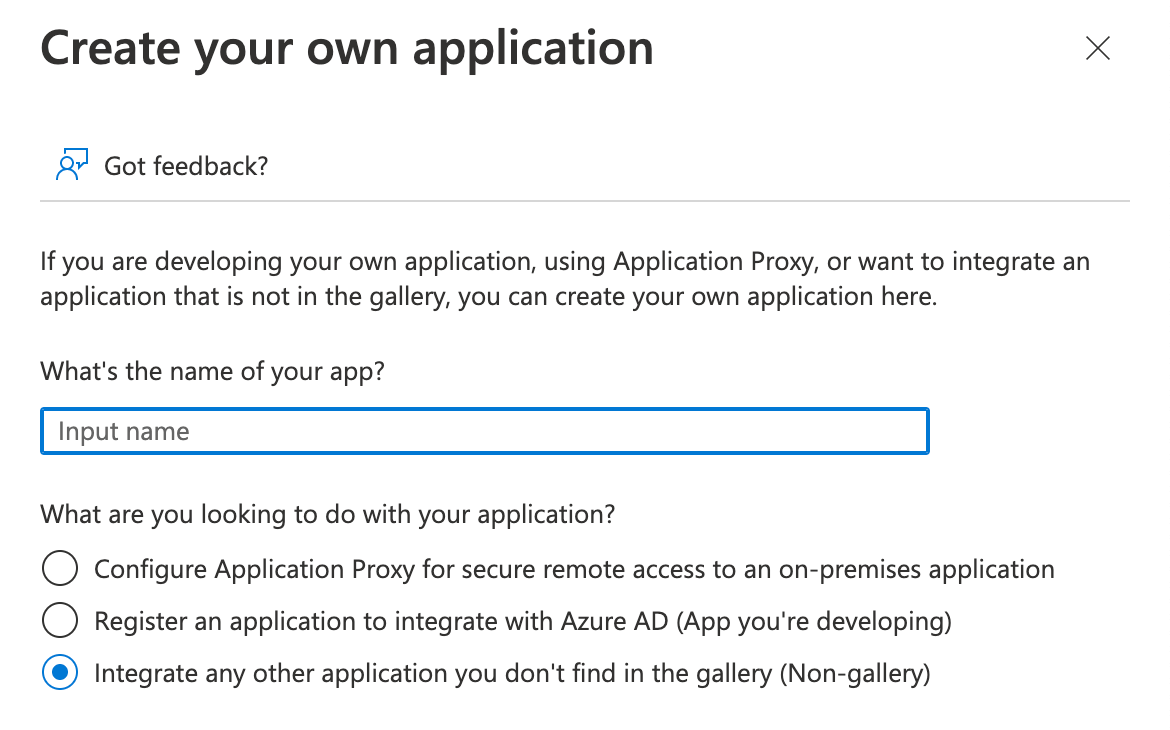
First, we need to create an enterprise application on Azure portal.
Log in to the portal, go to Azure Active Directory->Enterprise Applications->New application->Create your own application, enter DMARCLY as the name of the app, also make sure the "Integrate any other application you don't find in the gallery (Non-gallery)" option is selected, then hit Create, as illustrated below:
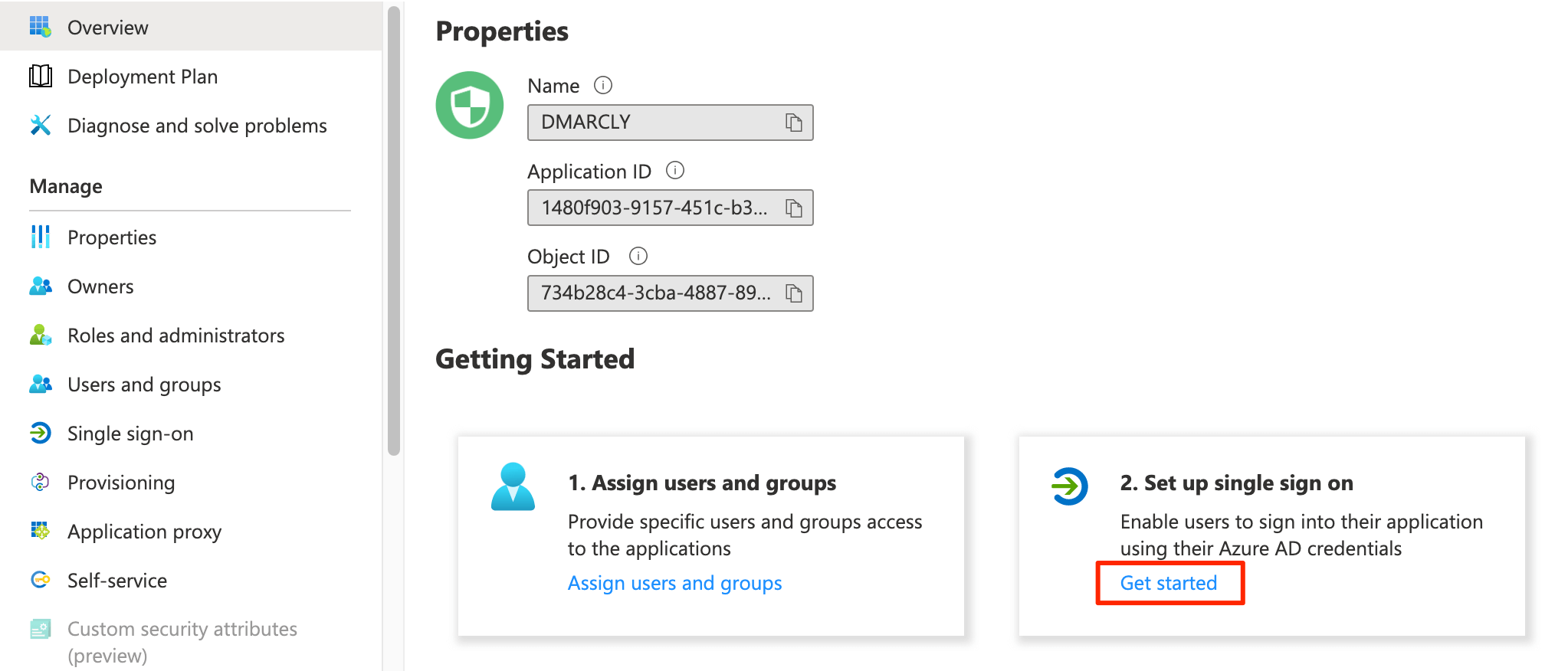
It may take Azure a while to create that application. Once the enterprise application is created, it will redirect to the Overview page of the application. If it's not the case, you need to navigate to the application list, and manually click on that application.
Configure the enterprise application for SSO
On the Overview page, click on Get started on the Set up single sign on card, as highlighted in red below:
Then it will display the SSO with SAML settings page.
Now you need to fill in Entity ID and Assertion Consumer Service URL on the Basic SAML Configuration card. Click on Edit on that card to reveal the Basic SAML Configuration modal:
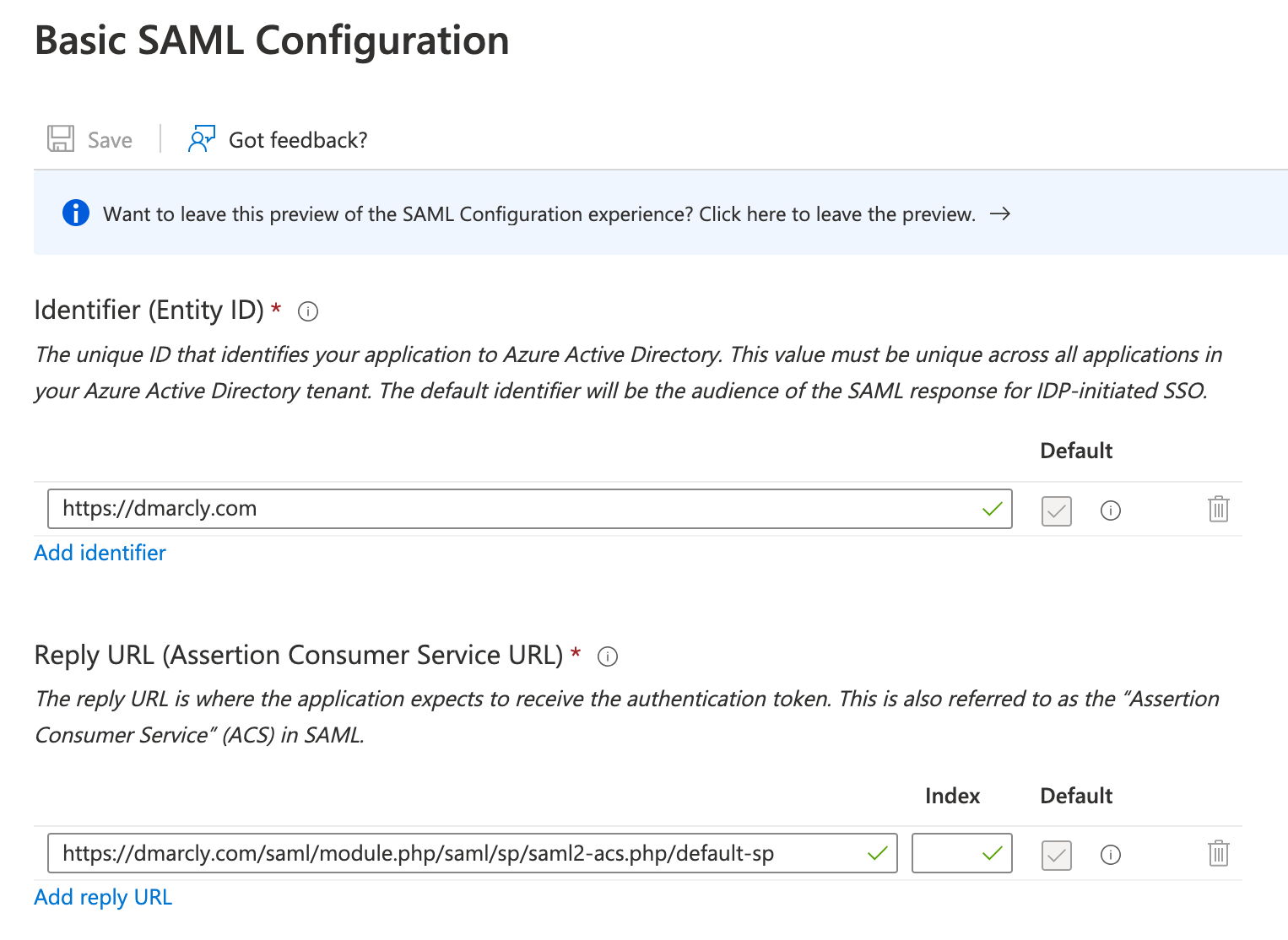
You need to grab Service Provider Entity ID and Assertion Consumer Service URL from the DMARCLY dashboard. Log in to DMARCLY, go to System->Single Sign-On (SSO), toggle on the Enable Single Sign-On switch, and choose Azure AD as the Identity Provider:
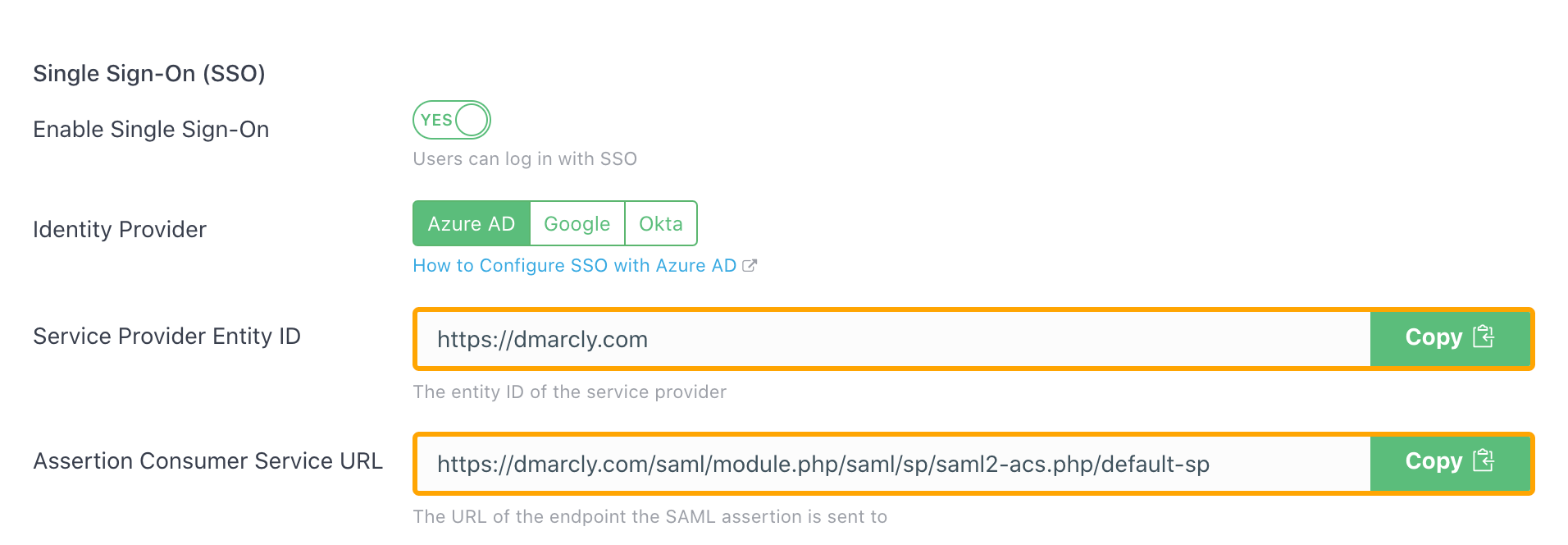
then copy these 2 values from there and paste them in the Azure portal input boxes one by one. Then hit Save.
Once done, it should look like this:
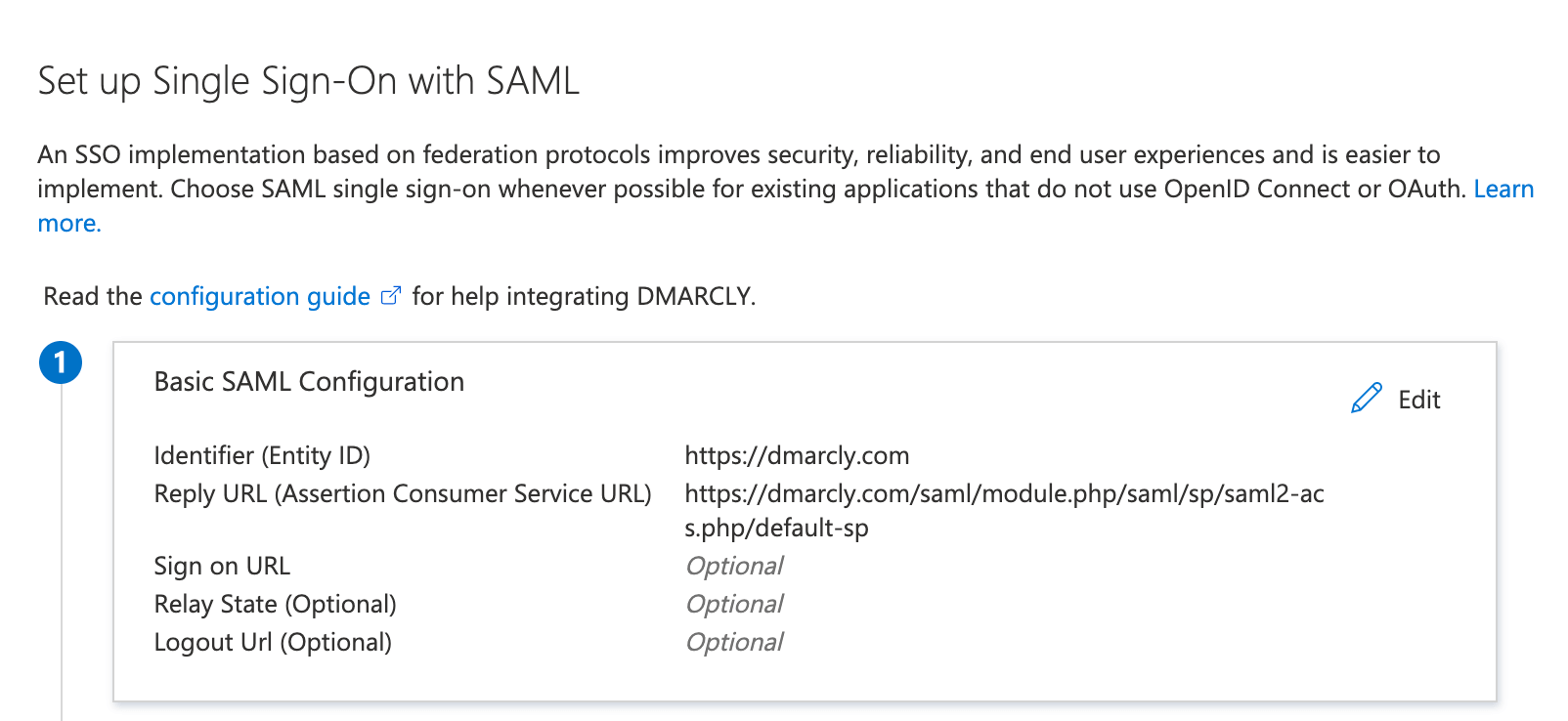
Note: if you are in the EU zone, please make sure that both Service Provider Entity ID and Assertion Consumer Service URL start with https://eu.dmarcly.com, instead of https://dmarcly.com.
Now scroll down to the SAML Certificates card on Azure portal, copy the App Federation Metadata Url value:
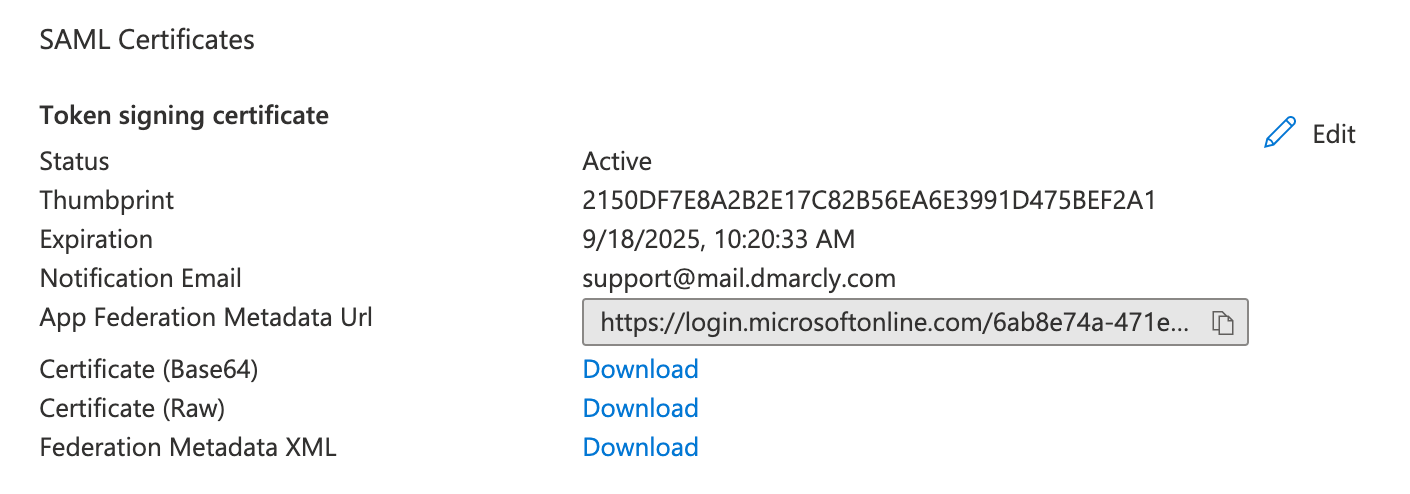
switch back to the DMARCLY dashboard, paste it in the IdP Metadata Url field:
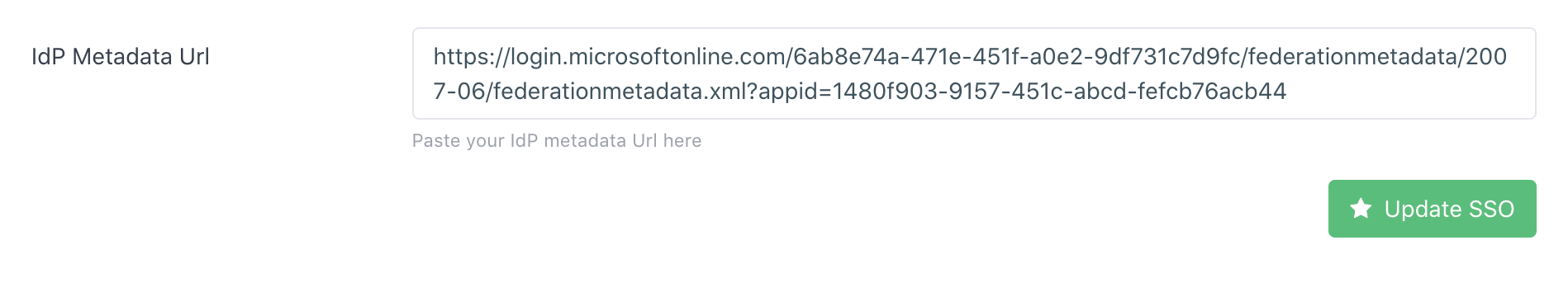
then hit Update SSO.
Assign users to the enterprise application
Before a user in your tenant can use the application, you must assign the user to it. Go to Azure Active Directory->Enterprise applications, click on the application to show its page, click on Users and groups, then click on Add user/group:
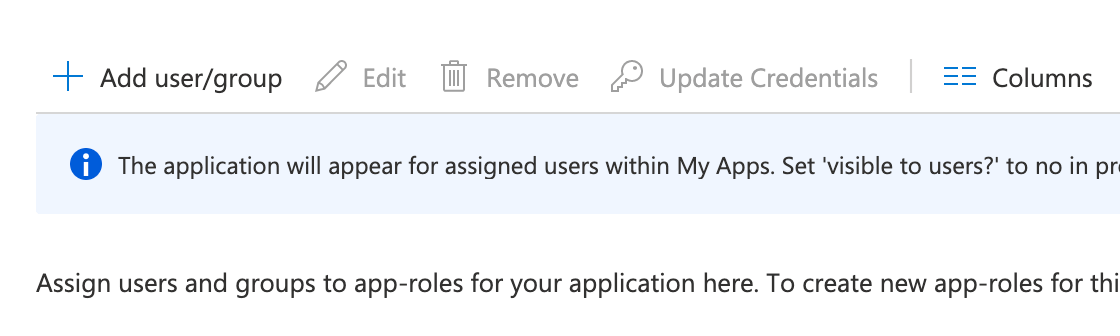
to open the Add Assignment page:
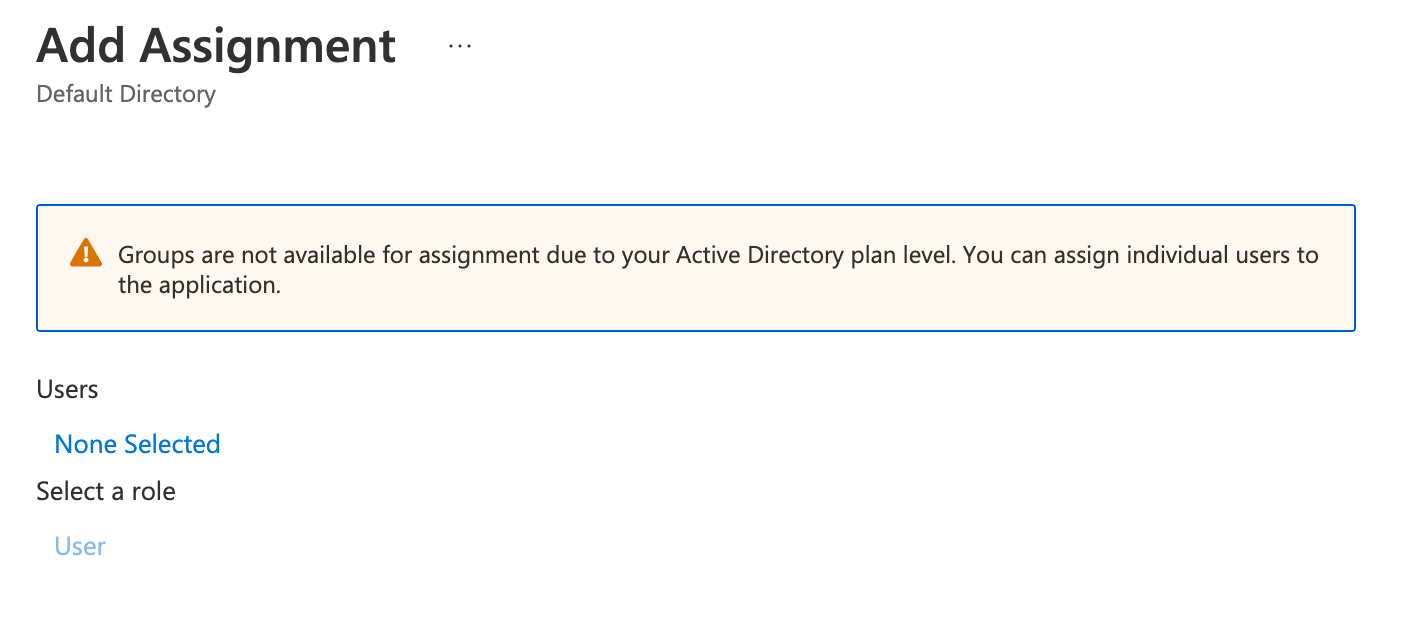
click on the Users row and follow the instructions to add the users. Then click on Assign.
Create users in DMARCLY
To log in via SSO, in addition to a corresponding user account in Azure AD, a user must have an account in DMARCLY.
To create a user account in DMARCLY, log in to the dashboard, go to Users->Add User, enter the user email address and the other fields on the page, then click on Save User.
Log in via SSO
Now that you are done with the configuration, you can log in via SSO.
If you are a non-EU user, navigate to https://dmarcly.com/login-sso, otherwise navigate to https://eu.dmarcly.com/login-sso.
Now enter your account email with DMARCLY, then you will be redirected to the Azure AD login screen:
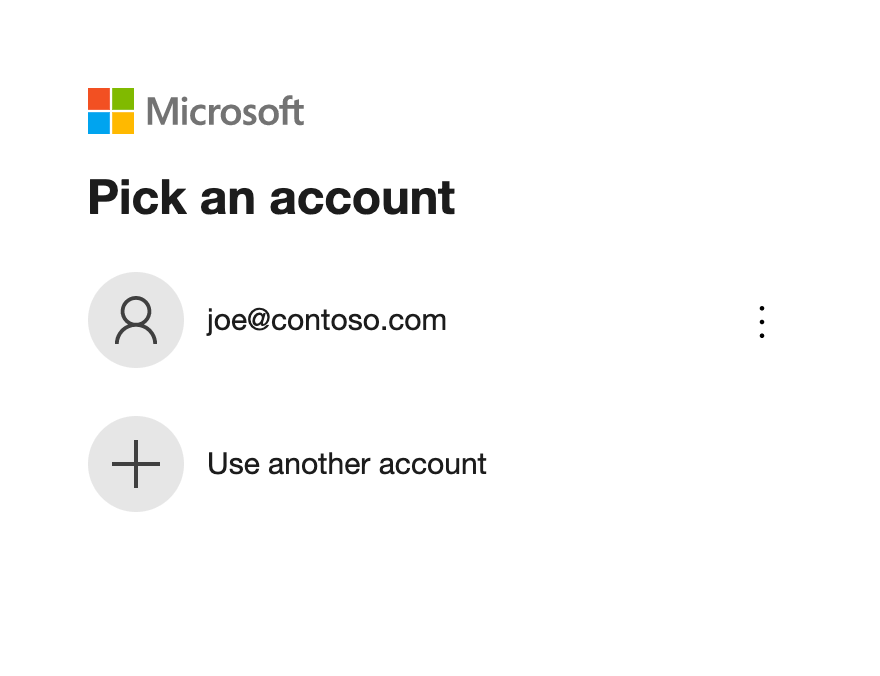
enter your credentials with Azure AD. Once authenticated, you will be redirected to the DMARCLY dashboard.
IdP-initiated SSO
You can also access DMARCLY directly from Microsoft. To do so, navigate to: https://myapps.microsoft.com, enter your credentials to log in, go to My Apps and you will see a list of applications created in Azure AD within your tenant.
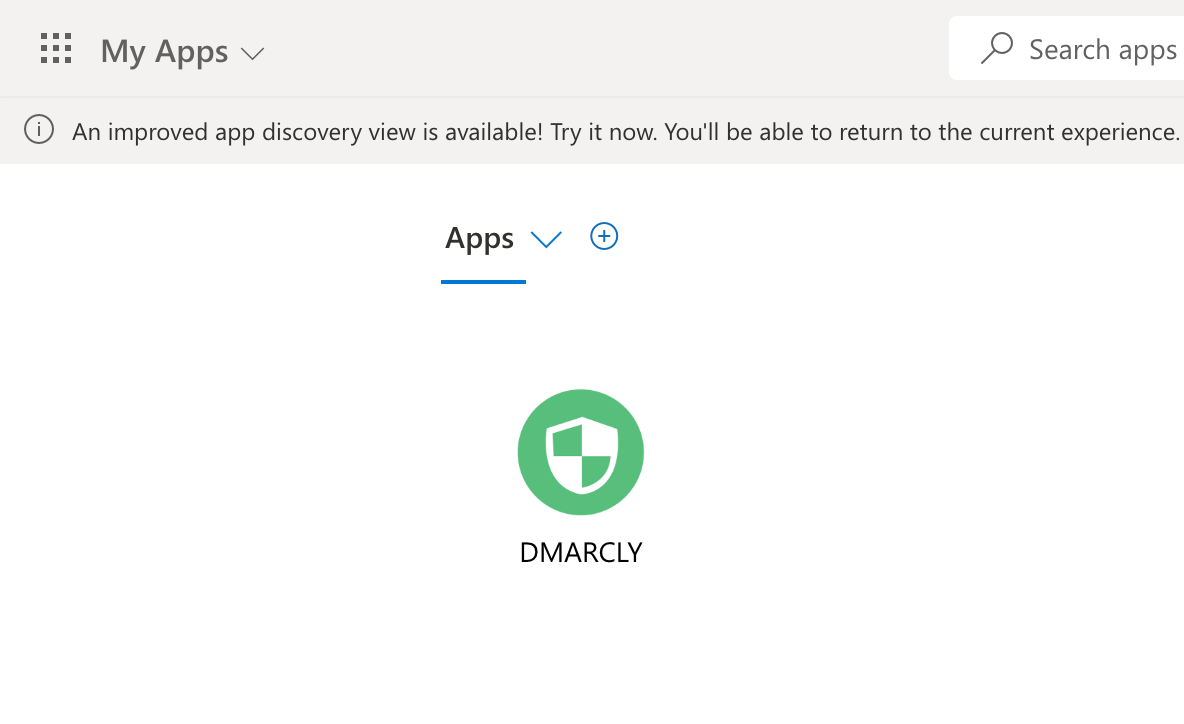
If you followed the steps above in this article, you will see the DMARCLY logo appear on that list. Simply click on the logo and you will be redirected to the DMARCLY dashboard.
Enforce SSO
You can enforce SSO so that all users must log in via SSO. That is, direct login will be disabled.
To enforce SSO, turn on the Enforce SSO checkbox in System->Single Sign-On (SSO) in the DMARCLY dashboard:
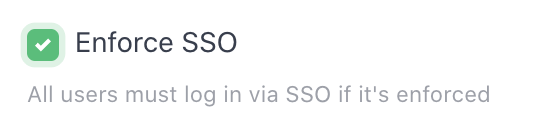
then click on Update SSO.
Now log out of your DMARCLY dashboard, and try to log in again on the direct login page, you will see some warning like this:
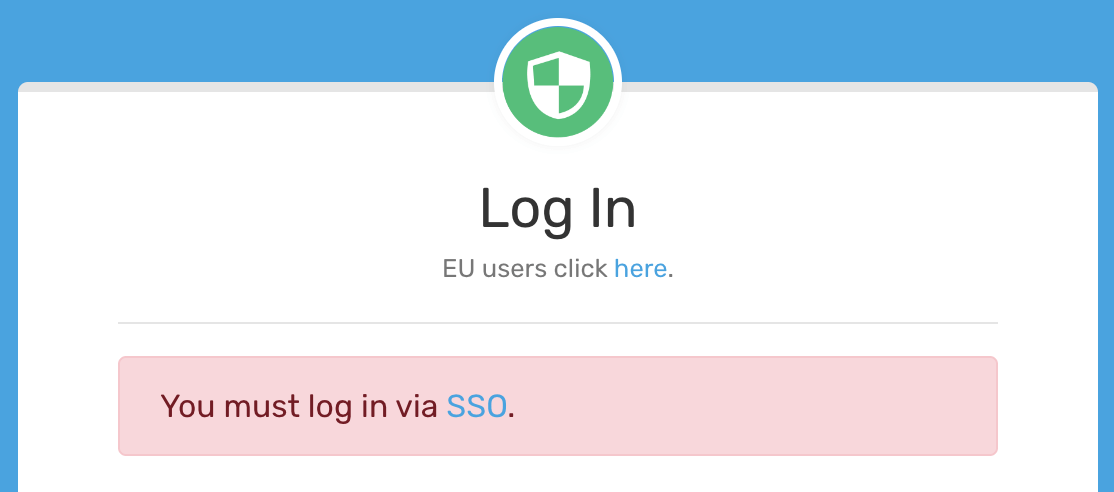
Simply click on the SSO link to proceed with SSO login.
Articolo precedente Prossimo articolo
Protect Business Email & Improve Email Deliverability
Get a 14 day trial. No credit card required.
Create Account